Distributed denial of service, more commonly known as DDoS attacks, is a growing cybersecurity concern for businesses these days. What is it, and how do you deal with it? This blog takes a deeper look at its meaning, complexity, forms, and prevention techniques.
What is DDoS Attack?
DDoS stands for Distributed Denial of Service. It is a tactic used by cybercriminals to make an organization’s website or online service inaccessible to its genuine users so that they can cause some tangible damage to their business or reputation. To perpetrate the DDoS attacks, attackers would inundate the target systems with thousands of service requests. As a result, the capacity of the systems would run out and stop responding.
What are the Key Differences Between DoS and DDoS?
DoS stands for Denial of Service, and DDoS stands for Distributed Denial of Service. The key differences between these two are given below:
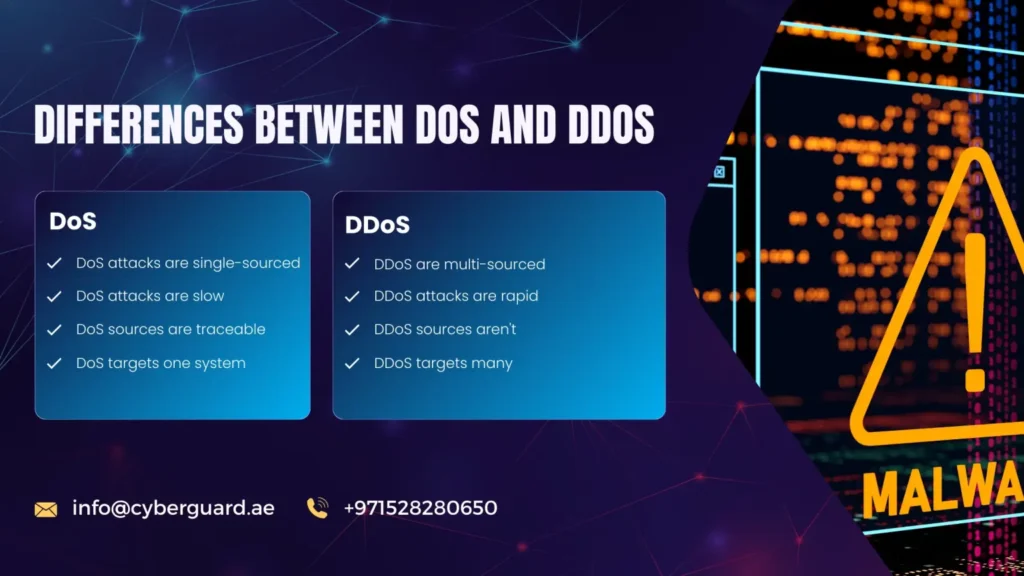
DoS:
- Attacks on the target systems come from a single source
- The attacks are slow-paced.
- It is easy to trace the source of DoS attacks.
- DoS attacks normally target a single system at first and take on other systems gradually.
- Since the attack starts with a single system, it is easy to identify it and prevent its spread to other systems.
DDoS:
- Attacks on the target systems come from numerous systems or sources.
- The attacks are rapid.
- It is difficult to trace the origin of DDoS attacks.
- Multiple systems, or the entire system of the organization, are attacked simultaneously.
- Since the attacks affect multiple systems simultaneously, isolating the attack turns out to be challenging.
How is DDoS Attack Carried Out?
DDoS attacks are carried out by causing the target website or online service to go out of service. The attacker would manipulate excessive traffic on the networks of these websites or online services using DDoS botnets or other congestion techniques to get this malicious task executed.
How to Detect a DDoS Attack?
Given the huge loss and reputational damage that DDoS attacks can cause to businesses, it is important to identify them at the onset and prevent them. Here are some common techniques to identify attack symptoms:

- Watch out for any patterns in user traffic, such as geolocation, specific types of devices, web browser versions, etc.
- Patterns of intermittent internet traffic—for instance, a surge of traffic every 20 minutes or increased user engagement at odd hours—could be a sign that perpetrators are on the loose.
- Keep regular track of your site visits using any reliable traffic analytics tools, and watch out for any unusual amount of traffic from suspicious IP ranges or particular IP addresses.
- Keep track of any excessive number of service requests to specific endpoints or pages on your website or online service. This could be a DDoS attack-traffic metaphor.
- Leveraging industry vulnerabilities specific to a business, perpetrators use a variety of DDoS attack tools to roll out initial connection requests and advance to more serious protocol attacks.
Typical Methods of DDoS Attacks
Distributed denial-of-service attacks occur in multiple varieties. The typical methods of these attacks are given below:
Protocol attacks:
Here the attacker identifies and exploits loopholes in protocols such as HTTP, DNS, or SMTP to cause resource exhaustion and advance to service disruption.
Transport Layer Attacks:
Lack of encryption with the connections that are used for API data transmission may allow the attackers to intercept or alter the data. It can lead to a lack of safety in the communication between the client and the API.
Application Layer Attacks:
The attacker tries to make web applications inaccessible by targeting resources like CPU or memory.
Network Layer Attacks:
By creating a high volume of state-exhaustion attacks, the attackers would consume the available network bandwidth, crashing the network equipment, which in turn would result in service disruption.
Volumetric Attacks:
A volumetric attack is the act of unleashing a high volume of traffic to flood systems or networks with the malicious intention of eating up the bandwidth and resources to ensure the denial of services for genuine users.
How to Prevent DDoS Attacks?
With effective DDoS mitigation strategies, it is possible to prevent distributed denial-of-service attacks. Here are some proven methods known for their effectiveness in DDoS protection.
- Given the probability of a DDoS attack website affecting your business, set up a practical defense strategy incorporating the best DDoS protection services. This should help you identify the symptoms at their onset and implement steps to mitigate them.
- Make proper use of your support solutions products, load balancers, etc. Make sure that you have the latest product releases from them to ensure their proper functioning. For instance, outdated Cloudflare DDoS protection won’t help in tackling the attacks.
- Keep a regular track of your systems and resources to identify any loopholes in security. Check for patterns of protocol attacks and unusual connection requests. Such proactive steps go a long way in assessing the security posture and working out quick DDoS mitigation.
- Provide your team with proper training on what to do in the event of a DDoS attack. Assign different responsibilities to your team, for instance, internet security, AWS DDoS protection, and DDoS prevention and remediation, to handle any unforeseen circumstances effectively.
Conclusion
In conclusion, the evolution of DDoS attacks highlights their growing sophistication and the need for strong anti-DDoS strategies. As these attacks continue to pose serious threats ranging from service disruptions to extortion attempts, businesses should rely on proactive defense measures to safeguard their digital infrastructures. We hope the points discussed in our blog have been informative to you. Please feel free to contact us for any assistance or inquiries you may have regarding distributed denial-of-service attacks and DDoS protection.
Frequently Asked Questions
In 2016, Dyn, the DNS provider for popular services like Twitter (currently X) and Netflix, was targeted by attackers using a botnet. This resulted in the flooding of their servers with heavy traffic, leading to a service disruption.
The immediate consequence of DDoS attacks is service disruption. Frequent attacks can lead to revenue loss, reputational damage, and compliance issues in the long run.
Cloudflare DDoS is a protection service that helps to mitigate DDoS attacks. From monitoring and filtering incoming traffic to detecting and preventing malicious connection requests, it helps keep your websites accessible to your legitimate users. Cloudflare DDoS protection prices vary depending on the services you opt for.
DDoS attacks are reported to last from a few minutes to several hours or weeks. The duration depends on the attacker’s ability to keep the outage undetected or unresolved by the victims.
Yes, conducting a DDoS attack is illegal in most countries, as it effectively violates cybercrime laws. Distributed denial-of-service attacks disrupt a business’s computer systems without their authorization. It is a criminal offence.
VPNs can prevent certain types of DDoS attacks as they help you keep your IP addresses hidden from the attackers and also allow for encrypting traffic. However, in several cases, for instance, volumetric attacks, VPNs aren’t very effective in stopping them.