What Is Web Application Penetration Testing and What Makes It So Essential?
Web application penetration testing is a procedure conducted to identify potential security vulnerabilities within a web application. During the testing, the tester will examine the website’s architecture, the environment where it is deployed and the codes it uses to pinpoint the vulnerable areas.
Penetration testing for web applications is significant for the following reasons:
- Frequent or periodical web application penetration testing is essential to ensure that the web application is safe for the users.
- In the context of frequent data breaches and cyberattacks on the web application, many governments require businesses to carry out web app penetration testing mandatorily.
- Businesses are required to comply with certain industry standards like HIPPA and PCI DSS, for which web application penetration testing is a requirement.
- By regularly conducting web application penetration testing organisations can demonstrate how committed they are to safeguarding users’ privacy and data security, earning their trust.
- Attempts to any common web application-focused attacks such as cross-site scripting and SQL injection can be discovered through web application pen testing.
- Security penetration testing targeted at web applications is the only way to verify whether the proposed features of the application are implemented in a secure environment.
- Pen testing involves special tests called ‘negative tests’ which identify and tell whether the system can be exploited to do something which it is not designed for.
- By conducting pen testing, businesses can stay ahead of cyberattacks and prevent risks and thus save a lot of money which otherwise would be required for recovery, litigation and other related expenses.
Understanding the Basics of Web Application Penetration Testing
Web application penetration testing is an important topic or area within the broad realm of cybersecurity. Let’s find out what it is, what common threats are and how to tackle them.
Meaning Of Basic Web Application Security?
Web application security refers to developing or ensuring a secure environment for web applications to operate. Web applications, like software, are not immune to cyberattacks. Hence, they need to be protected from all types of malicious attacks.
Common Web Application Vulnerabilities
Web applications, like websites, software and other computer systems, are susceptible to a range of vulnerabilities. Failure to address these vulnerabilities can result in more serious threats and attacks. Here are some common types of vulnerabilities.
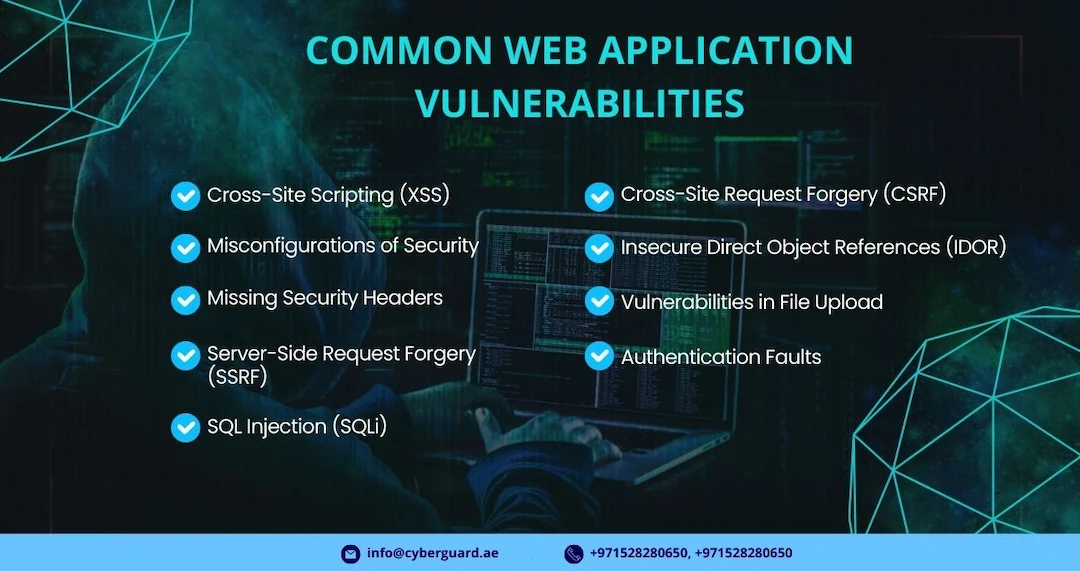
Cross-Site Scripting (XSS):
Cross-Site Scripting is the most common type of security vulnerability in web applications where an attacker injects faulty or malicious script into the web application through various methods. This leads to data or session compromises.
Misconfigurations of Security:
After some security loopholes are found, attackers will try to see if it is possible to configure the security settings to create unauthorized access to expose the data or to cause further security damage.
Missing Security Headers:
Insecure Deserialization happens as a result of handling serialised data wrongly. It leads to attackers gaining control over object structures, which they manipulate to get unauthorized access and then execute codes remotely.
Server-Side Request Forgery (SSRF):
Server-side request Forgery allows an attacker to gain access to the internal resources or the servers of a web application and exploit its ability to initiate requests originating from the web application
SQL Injection (SQLi):
SQL Injection is a type of vulnerability where a cyber attacker will initiate malicious SQL queries by manipulating the inputs. This leads to issues like data deletion, data modification and authorized access.
Cross-Site Request Forgery (CSRF):
Through Cross-Site Request Forgery, cybercriminals force genuine users to perform actions that they don’t intend to, without their knowledge.
Insecure Direct Object References (IDOR):
Attackers exploit vulnerabilities that enable them to manipulate references. Through this, they gain unauthorized access to forbidden resources or sensitive data.
Vulnerabilities in File Upload:
Here, the attacker exploits validation issues with file upload systems to upload malicious files into the servers. This will ultimately damage all the sensitive data in the system and its security.
Authentication Faults:
Attackers exploit weaknesses in users’ passwords or sessional management habits. By exploiting such vulnerabilities, they gain unauthorised access to the systems and initiate identity-related attacks.
Best Practices for Web Application Penetration Testing
To ensure that your penetration testing for web applications runs smoothly and yields the desired results, it is important to adhere to certain recommended practices. Here are the best practices for the same.
Verify authorization:
Before you initiate the tests, check whether the web application penetration testing companies you approach are licensed or have the required authorization for conducting the tests.
Know the application thoroughly:
Before conducting the tests, get to know the web application you are targeting for the penetration testing. Conducting tests without proper understanding will lead to failures.
Gather critical data:
Carry out a thorough reconnaissance to collect all required information about the application, its entry points you can advance for the tests and any other information about the infrastructure that might be useful.
Scan the application:
Scan the application to get an overview of the vulnerabilities present in it. It is recommended to scan using multiple tools rather than sticking to one as each tool is designed to pinpoint specific issues.
Test the application manually:
In addition to automated scanning and testing, it is recommended to test the application manually as well. This is typically done after the automated system identifies a vulnerability in the web application.
Analyse the loopholes:
Ongoing improvements of the systems are essential for organizations to stay immune to emerging threats. Black box pen testing gives insights about such emerging threats and allows for taking precautions.
Conduct session assessment:
Given that improver session management leads to several issues on web applications, analyse in what ways attackers can exploit active sessions and exploit such cases to evaluate the extent of attacks.
Perform real-world attacks:
Once a general level of understanding about the web application is gathered, simulate real-world attacks on it exploiting loopholes in authentication, authorization, file uploading, API security, security headers and other critical areas. .
Document the findings:
Document all the findings from your tests as well as what steps you performed to arrive at a certain conclusion, identify a certain vulnerability and exploit the same. This will enable the client to take safety measures in the future.
Communicate with Stakeholders
To ensure the success of a web application penetration testing session, proper communication and mutual understanding among all the stakeholders – developers, employees, cybersecurity team etc. – are essential.
Recommend ongoing improvements:
Suggest to the client what measures they can take to enhance the security controls, initiate ongoing improvements and expedite remediation efforts.
Common Challenges in web Application Penetration Testing
Web application penetration testing stands out as the go-to method for pinpointing vulnerabilities in web applications. However, it is worth noting that there are numerous challenges ahead of it and can backfire if not executed thoughtfully. Understanding the common difficulties is the first step in dealing with them.

Scope Definition Failure:
If the scope is not defined properly, it can affect the efficiency of the tests. To address this, make sure that there is a clear explanation as to the test boundaries and what components of the web application are to be tested.
Authorization Oversight:
It is risky to initiate a test without proper authorisations. Ensure that you have consent from the concerned parties before initiating any web application penetration testing. This not only helps maximum cooperation but also legal compliance.
Reconnaissance Shortcomings:
If the reconnaissance (collecting of relevant data) is insufficient, it can limit your understanding of the threat. Therefore, employ both automated tools and manual testing methods to scan and identify vulnerabilities and thereby have a proper information gathering or reconnaissance.
Overreliance on Automated Scanning:
Blind reliance on automated tools can leave your efforts unsuccessful. Besides automated scanning, carry out sufficient manual testing as well as to ensure that there is proper evaluation of the potential threats, especially of complex vulnerabilities.
Overlooking Business Logic Vulnerabilities:
Overlooking business logic threats exposes vulnerabilities and allows hackers to exploit them. To avoid it, include scenario-based testing where you can simulate real-world user interactions. This will help you reveal such business logic vulnerabilities in the web application security.
Resource-Intensive Nature:
Black box testing can be resource-intensive as it demands a significant amount of time, human resources and effort to conduct. This can lead to a compromise in the efficiency of this method.
Overlooks Logical Vulnerabilities:
Logical vulnerabilities refer to the flaws in the system due to misconfiguration or any other incorrect steps taken by people from the company or organization. In the black box pen testing method, the testers overlook or are not in a position to look into these types of vulnerabilities.
Input Validation Testing Gaps:
Insufficient validation of the inputs causes the vulnerabilities to be exposed to hackers. Conduct proper input validation during the pen testing to ensure the integrity of the data and thereby eliminate risks associated with injection attacks.
Overlooking Client-Side Security:
It has been noticed that overlooking client-side security enhances the chances of security risks. Hence, have a proper assessment of the client-side scripts and implement proper security controls following it.
Security Misconfigurations Oversight:
Given the high chances of vulnerability emerging from security misconfigurations, have regular auditing of these configurations. If any misconfigurations are noticed, address them straight away to fortify your web application security posture.
Limited Session Management Testing:
Limited session management testing can encourage hackers to compromise active user sessions. Test every session mechanism carefully to expose any weaknesses associated with them. Likewise, ensure that a recommended policy or practice is in place for the same.
Ineffective Reporting Practices:
Unless the findings are properly documented and reported to the stakeholders, no actions can be taken and thus diminish the impact of the tests as a whole. So clearly document and report your findings. Provide the clients with actionable steps to mitigate the problems to enhance their security posture.
Continuous Improvement and Monitoring
Having a pen test web application conducted alone won’t give you any edge over the threats. There must be an ongoing effort to keep track of emerging threats and improve your posture from time to time. Continuous monitoring of cyber threats contributes to enhanced cyber security. Doing so will give you the following benefits.
Improvement of productivity and efficiency:
By having ongoing monitoring in place, businesses can enhance their productivity and efficiency since it helps them optimize their processes and ensure smooth operations.
Improved quality:
When you have a web application giving maximum performance and reliability, you can rely on it like never before and think more about improving the quality standards rather than addressing the challenges.
Cost Savings:
Through continuous monitoring, you will have better chances to identify the risks at an early stage before they get intensified. This will effectively free you from paying a hefty amount to mitigate serious damage to the web applications.
Better Adaptability to Changes:
As new threats emerge; you are essentially required to adapt to new requirements. Continuous improvement facilitates better adaptability to the new changes you bring to your web application infrastructure.
More Engaged Workforce:
Ongoing monitoring and improvement practices of the web applications help you cultivate a more engaged workforce. An engaged workforce in a collaborative environment will essentially add to your business’s reputation, growth, and success.
Improved Customer Contentment:
Through consistent improvement practices, you can ensure improved customer satisfaction as you can provide them with a more reliable and secure web application experience. This, in turn, will nurture a loyal customer base who are ready to shower you with positive feedback.
Risk Mitigation:
Another great benefit of a continuous monitoring mechanism is that it minimizes risk as you are in a better position to promptly address any emerging vulnerability.
Strategic Alignment:
Ongoing monitoring will help you align your businesses’ broader objectives with the strategic goals you have in place. It will ensure that your web application security efforts are in alignment with those goals or strategies.
Informed business decisions:
Through a proper monitoring mechanism, you will have accurate data for informed decision-making. You will not have to rely on assumptions when it comes to choosing your web application’s security.
Competitive Edge:
Continuous improvement will enable you to incorporate the latest security practices into your web application security and thereby stay ahead of competitors. Moreover, it puts you in a better place to meet higher user expectations.
Conclusion
To recap, penetration testing for web applications is not merely a security measure; it’s a proactive step. It enables you to fortify the defence system of your web applications by reducing vulnerabilities and potential chances for exploitation. For a resilient digital environment, web application penetration testing is crucial.
Frequently Asked Questions
For a thorough web application penetration testing, which involves steps like scoping to recommending remediations, it usually takes anywhere from one week to a few weeks.
Yes. Finding a vulnerability and fixing it does not mean that you are fully insulated against emerging threats. Rescans will help you keep track of any new threats and address them before they get worse.
The cost of web application penetration testing depends on several factors such as the depth of the tests, complexity level, scope etc. It is recommended that you discuss your scope with a reliable web application pen testing company to get an exact quote.
web applications Penetration testing involves several steps. Start it by defining the scope of the test. This must follow gathering the relevant information and then analysing them, pinpointing the vulnerabilities and exploiting them, reporting and documenting and suggesting remediation.
Automated web application penetration testing refers to the use of automated tools to identify the vulnerability. While automated tools help identify the vulnerabilities easily, they will not help in analysing nuanced threats. So, automated testing should be supplemented with manual testing methods for maximum efficiency.
It is recommended to conduct regular penetration testing for web applications. Through frequent testing, you will learn about emerging threats and are in a better position to implement steps to address them. A minimum of annual testing is highly recommended.
After the penetration testing is concluded, the testing company will provide the client with a detailed report of the test – what steps they took, what vulnerabilities were assessed and exploited and remediation steps to address the vulnerabilities. Follow the remediation steps carefully as early as possible.
Web application penetration testing services focus on evaluating and analysing the security of web applications. They look at challenges specific to web applications, for instance, issues with input validation, session management, business logic vulnerabilities etc. On the other hand, normal pen testing services will focus on the entire infrastructure such as computer systems, networks, and other resources within their testing scope.